Ransomware - Prevention and Mitigation Best Practices
Ransomware prevention best practices per CISA and NIST CSF 2.0 - backup 3-2-1-1-0, MFA, segmentation, hardening, and incident response checklist.
In May 2023, CISA, the NSA, and the FBI published an updated #StopRansomware guide - a set of best practices for preventing ransomware attacks and mitigating their impact. In January 2025, NIST went further, publishing a Ransomware Risk Management Profile based on CSF 2.0. Both documents say the same thing: organizations that implement basic controls - offline backups, MFA, network segmentation - significantly reduce risk and recovery costs.
This article consolidates recommendations from both sources and supplements them with current data from 2025. If you are looking for the basics - what ransomware is, how it works, what the variants are - start with our ransomware guide. We discuss trends and the evolution of RaaS groups in a separate article.
Why prevention is cheaper than response
The cost of recovering from a ransomware attack far exceeds investments in security controls. Data from 2025 shows the scale of the disparity.
average operational downtime after an attack
average recovery cost (excluding ransom)
of identity-based attacks blocked by MFA
lower recovery costs with offline backup
Sources: Sophos State of Ransomware 2025, Microsoft Digital Defense Report 2025, Veeam Ransomware Trends 2025
The conclusion is simple: organizations that invest in prevention pay less - and recover faster. Below are specific practices, organized by attack vector and control area.
Incident preparedness - fundamentals
Before addressing prevention of specific vectors, two areas require the attention of every organization regardless of industry and size.
Backups - the 3-2-1-1-0 rule
The traditional 3-2-1 rule (3 copies, 2 media, 1 offsite) is no longer sufficient. Attackers target backup infrastructure in 96% of cases - if the backup is accessible with the same credentials as production systems, it becomes another encryption target.
The current CISA recommendation and industry standard is the 3-2-1-1-0 rule:
| Element | Meaning | Why it matters |
|---|---|---|
| 3 copies | Production data + 2 backup copies | Redundancy protects against single media failure |
| 2 media | Two different media types (disk + cloud, disk + tape) | Failure of one type does not destroy all copies |
| 1 offsite | One copy at a different location | Protection against fire, flood, physical destruction |
| 1 immutable | Immutable copy (WORM/object lock) | Ransomware cannot encrypt or delete it |
| 0 errors | Daily monitoring + regular recovery tests | Backup with errors = false sense of security |
WARNING
Organizations with immutable backups report 90% shorter recovery times than those without. WORM (Write Once, Read Many) technologies are available from most cloud providers - AWS S3 Object Lock, Azure Immutable Blob Storage, Wasabi Object Lock. Deployment does not require large budgets, but it does require deliberate configuration.
Additional CISA recommendations:
- Maintain encrypted Golden Image copies of critical systems (virtual machines, servers) - enables rapid rebuild
- Use Infrastructure as Code (IaC) to restore cloud resources from versioned templates
- Keep offline copies of source code, licenses, and IT asset documentation
- Consider a multi-cloud solution to avoid dependency on a single provider
Incident response plan
Before an attack occurs, the organization must have a ready, practiced cyber incident response plan (IRP). CISA recommends:
- Clearly defined notification procedures (who, when, through which channel)
- Regular exercises (tabletop exercises) - at least once a year
- Paper and offline versions of the plan - during an attack, IT systems may be unavailable
- Inclusion of crisis communication - informing the board, regulator, insurer
TIP
NIST IR 8374r1 (Ransomware Risk Management Profile) maps each of the above controls to specific CSF 2.0 functions: Govern (GV), Identify (ID), Protect (PR), Detect (DE), Respond (RS), Recover (RC). Use this profile as a checklist when building your ransomware protection program.
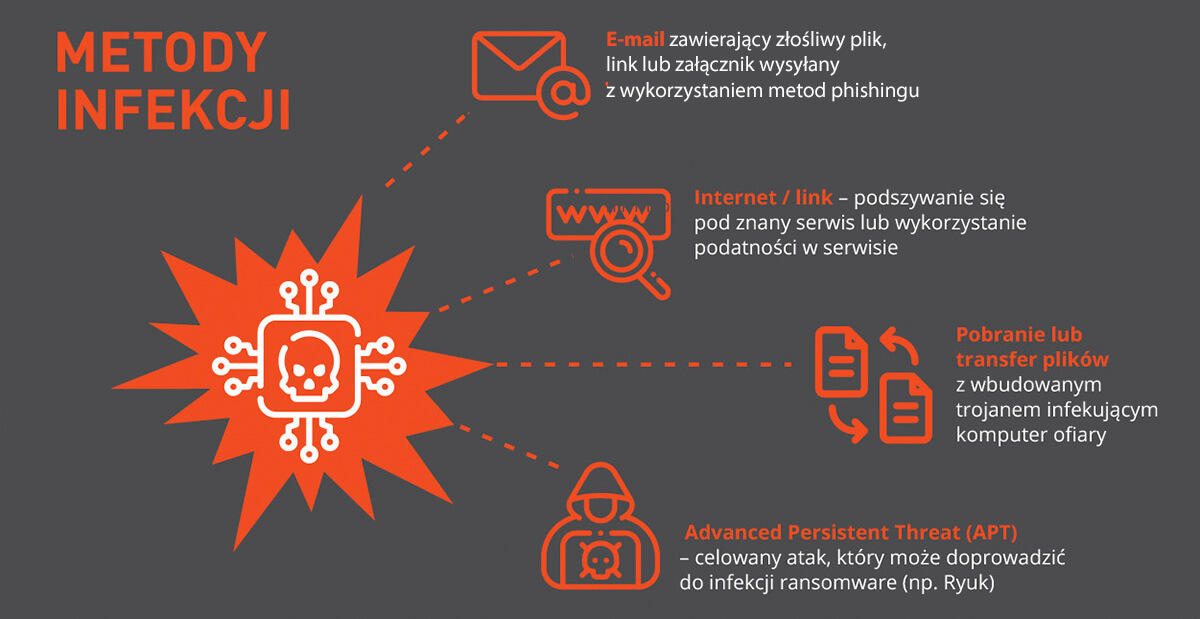
Prevention - by initial access vector
Best practices for prevention are organized by the typical ways attackers gain initial access to the network.
Vulnerabilities and misconfigurations
This vector is responsible for approximately 30% of successful ransomware attacks. WannaCry had a patch available for a month, Colonial Pipeline - a VPN account without MFA.
Key controls:
- Regular vulnerability scanning, with priority for internet-facing systems
- Critical patches within 48 hours - especially for VPN, RDP, browsers, document readers
- Disable unnecessary ports and protocols (RDP on port 3389, SMBv1/v2 - migrate to SMBv3)
- Cloud configuration audit, mobile devices, and BYOD
- Update VPN with the latest patches and enable MFA on all connections
NOTE
If RDP is essential, apply: regular audits of systems using RDP, close unused ports, enforce account lockout after several failed attempts, MFA, detailed connection attempt logging. Consider Windows Defender Remote Credential Guard and restricted admin mode.
Compromised credentials
Stolen passwords account for approximately 20% of entry vectors. IABs (Initial Access Brokers) sell ready-made access on the dark web for $500-$50,000.
Security checklist:
- Phishing-resistant MFA on all services - email, VPN, critical accounts
- Assess the feasibility of deploying passwordless authentication (biometrics, FIDO2 keys, device PIN)
- Dark web monitoring for leaked organizational credentials
- Deploy an IAM system for role and permission management
- Password policy: minimum 15 characters, unique, stored in a secure password manager
- Automatic account lockout after several failed attempts + logging and monitoring
- Separation of administrative accounts from daily-use accounts
- Disable password saving in browsers (Group Policy)
- Quarterly account audits - identify inactive accounts, excessive permissions, third-party access
Phishing and social engineering
This is the most effective vector - approximately 45% of ransomware attacks begin with an email.
Technical mechanisms:
- Flag external emails in the mail client
- Gateway filtering: block known malicious indicators, suspicious IP addresses
- Attachment filters - block file types most commonly used for malware delivery
- Deploy DMARC + SPF + DKIM - protection against domain spoofing
- Disable macros in Office files sent via email
- Disable Windows Script Host (WSH)
Human factor:
- Regular phishing awareness training - not once a year, but continuous
- Controlled phishing campaigns as part of penetration testing
- Protective DNS blocking malicious domains at the source
- Sandbox browsers isolating browsing sessions from the operating system
Precursor malware and advanced threats
Ransomware is rarely the first malware in a network. It is often preceded by droppers - Bumblebee, Emotet, QakBot - that prepare the ground for the main attack.
Multi-layered defense:
- Centrally managed antivirus with automatic signature updates
- EDR (Endpoint Detection and Response) on all workstations and servers
- IDS (Intrusion Detection System) to identify C2 communication
- Windows Sysmon monitoring for suspicious processes
- Application whitelisting - only authorized software can execute
Third parties and managed service providers (MSPs)
Managed service providers are an infection vector that can affect multiple clients simultaneously. The Kaseya attack (2021) affected over 1,500 organizations through a single MSP.
- Assess supplier security practices before granting access
- Principle of least privilege - access only to systems necessary for the supplier’s role
- Service Control Policies (SCP) in the cloud - restrict the ability to delete logs, modify VPCs
- Regular audits of third-party access
Infrastructure hardening - general best practices
Beyond vector-specific controls, CISA recommends a set of hardening practices that reduce the attack surface regardless of the entry method.
Asset management
You cannot protect what you do not know about. Detailed IT asset inventory - both hardware and logical - enables prioritization of protection and recovery. More on the approach to asset inventory in industrial networks.
Principle of least privilege
- Restrict user permissions for installing and running applications
- Block remote access for local accounts (Group Policy)
- Regular Active Directory audits - excessive permissions, Protected Users groups
- Windows Defender Remote Credential Guard for RDP sessions
Hypervisor protection
There is a growing trend of attacking VMware ESXi servers, which enable rapid encryption of entire infrastructure at scale. Keep hypervisors and networking/storage components updated.
Cloud security
- Regular backups - offline or cloud-to-cloud
- Activity logging on all resources with anomaly alerts
- Object lock / deletion protection on storage resources
- Object versioning in storage
- API request signing with custom programmatic access
Remote access tool control
- Audit RMM (Remote Monitoring and Management) tools in the network
- Analyze logs for unusual usage patterns or portable executables
- Enforce use of only authorized RMM solutions through VPN/VDI
- Block unauthorized RMM connections at the network level
Zero Trust architecture and segmentation
ZTA deployment and network segmentation - both physical and logical - are recommended by both CISA and NIST CSF 2.0. Segmentation limits an attacker’s lateral movement and isolates the impact of a breach. We discuss the detailed approach to network segmentation in OT environments in a separate article.
Additional controls:
- Restrict PowerShell to selected users (Group Policy)
- Update to the latest PowerShell version with module, script block, and transcription logging enabled
- Secure domain controllers (DCs) - latest Windows Server, regular patches, minimal software, no internet access, PAM, LSA protection
- Central log system (SIEM) with a minimum 12-month retention
- Baseline network traffic analysis and anomaly detection configuration
Ransomware attack response checklist
If an organization has fallen victim to ransomware, the following steps - based on the CISA #StopRansomware guide - should be executed in order.
Phase 1: Detection and isolation
- Identify affected systems and immediately disconnect them from the network (Ethernet/Wi-Fi)
- If multiple systems are affected, consider disconnecting the entire network at the switch level
- Do NOT power off infected machines - decryption keys may be in RAM
- Communicate via out-of-band channels (phone) - attackers may be monitoring email
- In the cloud: take volume snapshots as forensic evidence
- Prioritize isolation of business-critical systems
Phase 2: Assessment and analysis
- Look for traces of precursor malware (Emotet, QakBot, Cobalt Strike)
- Check for newly created AD accounts and privilege escalations
- Monitor VPN, RDP, PowerShell, PsTools anomalies
- Look for signs of data exfiltration (Rclone, FTP, cloud services)
- Check for Volume Shadow Copy modifications, backup configuration, boot changes
- Identify the ransomware variant - NoMoreRansom.org may have a free decryptor
- In the cloud: monitor IAM changes, firewall rules, resource security
Phase 3: Notification
- Inform internal and external teams according to the IRP
- Report the incident to the appropriate regulatory body (CERT, financial regulator - depending on sector)
- Coordinate public communication with PR
- Inform the cyber insurer
Phase 4: Containment and eradication
- Preserve evidence - system memory, security logs, firewall buffers
- Seek advice from ransomware specialists and legal counsel
- Terminate execution of identified ransomware binaries
- Identify persistence mechanisms (outside-in and inside-out)
- Reset passwords for all affected systems
- Deactivate VPN, remote access servers, SSO, and public-facing resources
Phase 5: Recovery
- Restore systems from encrypted offline copies - prioritize by criticality
- Clean VLAN for recovery - attach only verified systems
- Deploy patches and updates that may have been previously missed
- Document lessons learned and update the IRP
WARNING
Paying the ransom does not guarantee data recovery and funds further attacks. CISA, the FBI, Europol, and CERT recommend: do not pay. Instead, invest in backup infrastructure and an incident response plan - that is the only guarantee of restoring operations.
Mapping to NIST CSF 2.0
NIST IR 8374r1 (January 2025) maps ransomware prevention controls to the six CSF 2.0 functions. Key mappings below:
| CSF 2.0 Function | Controls from this article |
|---|---|
| Govern (GV) | Security policies, third-party risk management, training program |
| Identify (ID) | Asset inventory, dependency analysis, critical system identification |
| Protect (PR) | MFA, segmentation, hardening, backup 3-2-1-1-0, ZTA, access control |
| Detect (DE) | EDR, IDS, SIEM, anomaly monitoring, canary files, log analysis |
| Respond (RS) | Response plan, system isolation, forensics, notification |
| Recover (RC) | Restoration from backups, system rebuild, lessons learned |
Summary
Ransomware prevention rests on a few fundamental controls that CISA and NIST have repeated for years - because they work:
- Backup 3-2-1-1-0 with an immutable copy and regular recovery tests
- Phishing-resistant MFA at every remote access point
- Network segmentation limiting attacker lateral movement
- Patching within 48 hours of critical vulnerabilities on internet-facing systems
- A practiced response plan with an offline version and regular exercises
None of these controls are new. But data from 2025 shows that organizations that implement them consistently pay an average of $750,000 for recovery instead of the $3 million demanded ransom - and regain operations in days, not weeks.
SEQRED helps organizations verify the effectiveness of these controls in practice - through penetration tests and Red Team operations that simulate real ransomware attack scenarios.
Sources
- CISA #StopRansomware Guide (October 2023, updated March 2025)
- NIST IR 8374r1 - Ransomware Risk Management: CSF 2.0 Community Profile (January 2025)
- NIST Cybersecurity Framework 2.0 (February 2024)
- Sophos State of Ransomware 2025
- Veeam Ransomware Trends Report 2025
- Microsoft Digital Defense Report 2025
- NoMoreRansom.org - free decryptors