Compliance & Audits
We protect the industrial control systems that power your business
We support industrial infrastructure operators in securing SCADA, DCS and PLC controller networks - from identifying critical assets through architecture audit to continuous monitoring with Nozomi Networks.
Last updated: April 2026
OT Security is a SEQRED service covering audit, monitoring and protection of scada, dcs and plc controller networks.
Compliance & Audits
OT environments operate under different priorities than IT: availability and human safety come first, maintenance windows are limited, and many systems run on platforms that cannot be easily updated. At the same time, connections between corporate and industrial networks are growing, and attacks on OT infrastructure are no longer theoretical. Organizations need a partner who understands these constraints, can work passively and improve security without jeopardizing production continuity.
Scope
Crown jewel analysis - identification and prioritization of most critical OT assets
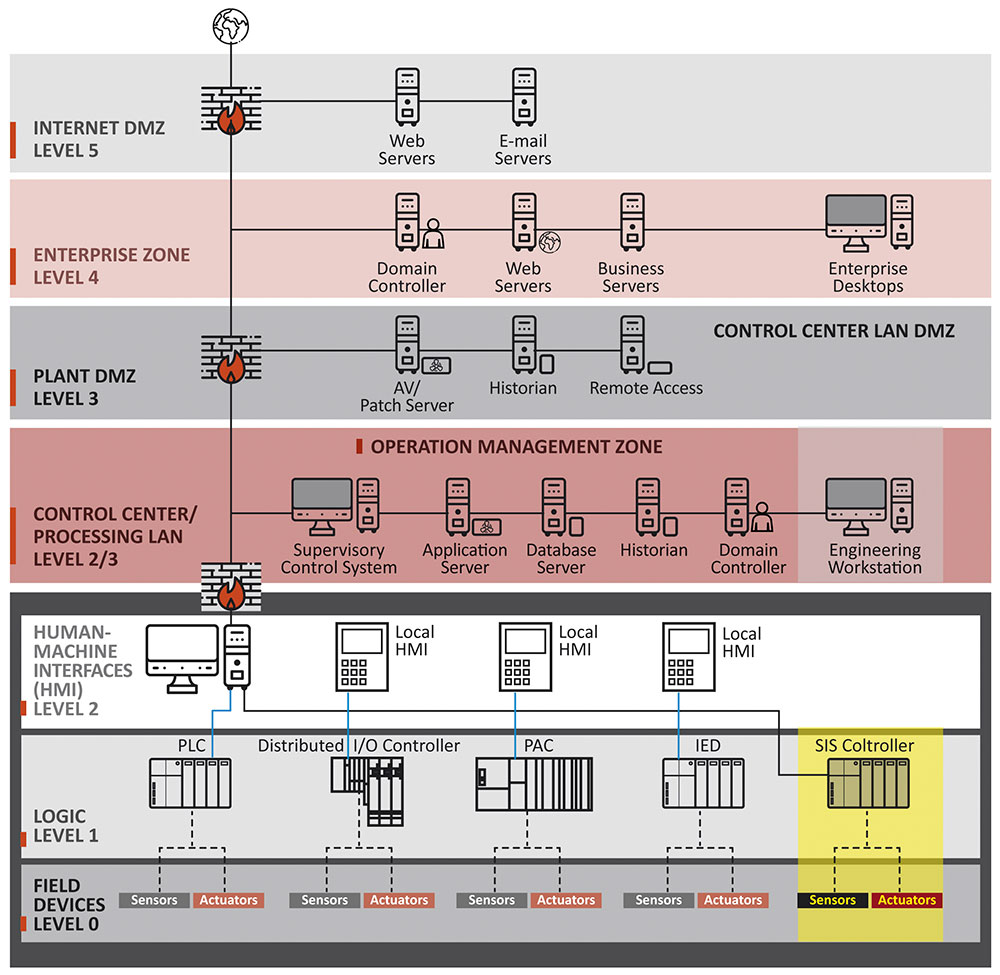
OT network architecture and segmentation audit (Purdue model, IEC 62443 zones and conduits)
Passive inventory and classification of OT assets (Siemens, Schneider Electric, Honeywell, Emerson, ABB)
SCADA system configuration assessment (Wonderware, iFIX, WinCC) and DCS
Device and protocol security testing (Modbus, OPC UA, DNP3, IEC 61850, PROFINET)
Passive OT network monitoring deployment (Nozomi Networks Guardian/Vantage)
Tabletop exercises - OT incident simulation with the client's team
OT security policies, procedures and incident response plan development
Process
Inventory and assessment
We map the OT environment: devices, protocols, data flows, and IT network touchpoints.
Architecture audit
We evaluate segmentation, access control, firewall configurations, and DMZ zones.
Risk identification
We prioritise vulnerabilities considering the impact on production continuity and human safety.
Recommendations and implementation
We deliver a remediation plan and support implementation: segmentation, monitoring, hardening.
Continuous monitoring
On request, we deploy and maintain a Nozomi Networks solution for OT network anomaly monitoring.
Related articles
DDoS Attacks on Industrial Infrastructure - Threats and Protection
DDoS attacks on OT/ICS systems - vectors, incidents (Killnet, NoName057), critical infrastructure protection, and NIS2 requirements.
Sabotage and Human Error - Underestimated Threats in OT Environments
Insider threats and human error in OT - incidents, statistics, and 12 organizational controls based on IEC 62443.
USB Removable Media Security in ICS Networks - Threats and Controls
USB threats in OT environments - malware, sabotage, data exfiltration. IEC 62443 controls, security kiosk, and policies.
FAQ
Can an OT audit disrupt production systems? +
We use passive methods (network traffic listening) and agree with the client on every active action. Production continuity is the priority.
Which OT platforms do you support? +
We have experience with Siemens (SIMATIC, WinCC), Schneider Electric (EcoStruxure), Honeywell (Experion), Emerson (DeltaV), ABB, Allen-Bradley, and others.
What is Nozomi Networks and why do you recommend it? +
Nozomi Networks is a platform for passive OT/IoT network monitoring - it detects anomalies, unauthorised devices, and known vulnerabilities without affecting system operation.
How does the collaboration with our OT maintenance team work? +
We work closely with the client's automation engineers - every change is consulted and planned around maintenance windows.
Do you offer ongoing OT monitoring? +
Yes - we can deploy and maintain a monitoring solution or train the client's team for independent operation.
How does SEQRED price its services? +
Pricing is based on an individual estimate of our consultants' time, considering the project scope and complexity. We present the offer broken down by phases - so you see exactly what you're paying for and can make decisions at each stage.
Can I speak with an expert before making a decision? +
Yes - an initial consultation is always welcome and free of charge. We help define the actual scope of your needs, which allows us to prepare a rational offer tailored to your organization.
How are OT security projects priced? +
Cost depends on the number of OT assets, number of industrial locations, and the scope of monitoring to be deployed. We help match the service scope to the size and specifics of your infrastructure.
We'll discuss scope, methodology, and timeline.
Free consultation, no strings attached.
